
Whistleblower Says Microsoft Left US Govt Hackable
This story was originally published by ProPublica , a Pulitzer Prize-winning investigative newsroom.
Microsoft hired Andrew Harris for his extraordinary skill in keeping hackers out of the nation's most sensitive computer networks. In 2016, Harris was hard at work on a mystifying incident in which intruders had somehow penetrated a major US tech company.
The breach troubled Harris for two reasons. First, it involved the company's cloud - a virtual storehouse typically containing an organization's most sensitive data. Second, the attackers had pulled it off in a way that left little trace.
He retreated to his home office to“war game” possible scenarios, stress-testing the various software products that could have been compromised.
Early on, he focused on a Microsoft application that ensured users had permission to log on to cloud-based programs, the cyber equivalent of an officer checking passports at a border. It was there, after months of research, that he found something seriously wrong.
The product, which was used by millions of people to log on to their work computers, contained a flaw that could allow attackers to masquerade as legitimate employees and rummage through victims'“crown jewels” - national security secrets, corporate intellectual property, embarrassing personal emails - all without tripping alarms.
To Harris, who previously had spent nearly seven years working for the US Defense Department, it was a security nightmare. Anyone using the software was exposed, regardless of whether they used Microsoft or another cloud provider such as Amazon. But Harris was most concerned about the federal government and the implications of his discovery for national security. He flagged the issue to his colleagues.
They saw it differently, Harris said. The federal government was preparing to make a massive investment in cloud computing, and Microsoft wanted the business. Acknowledging this security flaw could jeopardize the company's chances, Harris recalled one product leader telling him. The financial consequences were enormous. Not only could Microsoft lose a multibillion-dollar deal, but it could also lose the race to dominate the market for cloud computing.
Harris said he pleaded with the company for several years to address the flaw in the product, a ProPublica investigation has found. But, at every turn, Microsoft dismissed his warnings, telling him they would work on a long-term alternative - leaving cloud services around the globe vulnerable to attack in the meantime.
Harris was certain someone would figure out how to exploit the weakness. He had come up with a temporary solution, but it required customers to turn off one of Microsoft's most convenient and popular features: the ability to access nearly every program used at work with a single logon.
He scrambled to alert some of the company's most sensitive customers about the threat and personally oversaw the fix for the New York Police Department. Frustrated by Microsoft's inaction, he left the company in August 2020.
Within months, his fears became reality. US officials confirmed reports that a state-sponsored team of Russian hackers had carried out SolarWinds, one of the largest cyberattacks in US history.
They used the flaw Harris had identified to vacuum up sensitive data from a number of federal agencies – including, ProPublica has learned, the National Nuclear Security Administration, which maintains the United States' nuclear weapons stockpile, and the National Institutes of Health, which at the time was engaged in Covid-19 research and vaccine distribution.
The Russians also used the weakness to compromise dozens of email accounts in the Treasury Department, including those of its highest-ranking officials . One federal official described the breach as“an espionage campaign designed for long-term intelligence collection.”
Harris' account, told here for the first time and supported by interviews with former colleagues and associates as well as social media posts, upends the prevailing public understanding of the SolarWinds hack.
From the moment the hack surfaced, Microsoft insisted it was blameless. Microsoft President Brad Smith assured Congress in 2021 that“there was no vulnerability in any Microsoft product or service that was exploited” in SolarWinds.
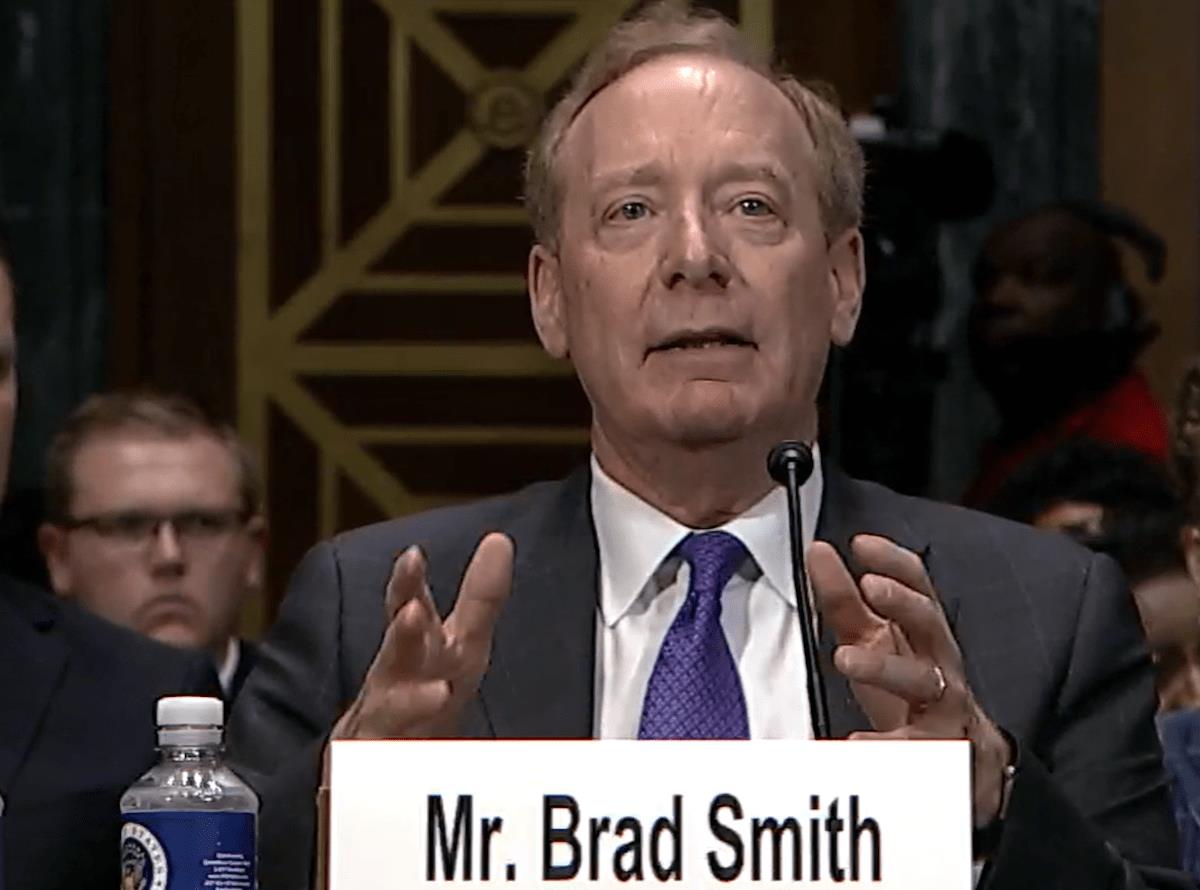
Microsoft President Brad Smith testifies in 2023 before the U.S. Senate Judiciary Committee Subcommittee on Privacy, Technology, and the Law. Photo: Screenshot via webcast / GeekWire
He also said customers could have done more to protect themselves.
Harris said they were never given the chance.
“The decisions are not based on what's best for Microsoft's customers but on what's best for Microsoft,” said Harris, who now works for CrowdStrike, a cybersecurity company that competes with Microsoft.
Microsoft declined to make Smith and other top officials available for interviews for this story, but it did not dispute ProPublica's findings. Instead, the company issued a statement in response to written questions.
“Protecting customers is always our highest priority,” a spokesperson said.“Our security response team takes all security issues seriously and gives every case due diligence with a thorough manual assessment, as well as cross-confirming with engineering and security partners. Our assessment of this issue received multiple reviews and was aligned with the industry consensus.”
ProPublica's investigation comes as the Pentagon seeks to expand its use of Microsoft products - a move that has drawn scrutiny from federal lawmakers amid a series of cyberattacks on the government.
Smith is set to testify on Thursday before the House Homeland Security Committee , which is examining Microsoft's role in a breach perpetrated last year by hackers connected to the Chinese government. Attackers exploited Microsoft security flaws to gain access to top US officials' emails. In investigating the attack, the federal Cyber Safety Review Board found that Microsoft's“security culture was inadequate and requires an overhaul.”
For its part, Microsoft has said that work has already begun, declaring that the company's top priority is security“above all else.” Part of the effort involves adopting the board's recommendations.“If you're faced with the tradeoff between security and another priority, your answer is clear: Do security,” the company's CEO, Satya Nadella, told employees in the wake of the board's report, which identified a“corporate culture that deprioritized both enterprise security investments and rigorous risk management.”
ProPublica's investigation adds new details and pivotal context about that culture, offering an unsettling look into how the world's largest software provider handles the security of its own ubiquitous products. It also offers crucial insight into just how much the quest for profits can drive those security decisions, especially as tech behemoths push to dominate the newest - and most lucrative - frontiers, including the cloud market.
“This is part of the problem overall with the industry,” said Nick DiCola, who was one of Harris's bosses at Microsoft and now works at Zero Networks, a network security firm. Publicly-traded tech giants“are beholden to the share price, not to doing what's right for the customer all the time. That's just a reality of capitalism. You're never going to change that in a public company because at the end of the day, they want the shareholder value to go up.”
A“Cloud-First World”Early this year, Microsoft surpassed Apple to become the world's most valuable company, worth more than $3 trillion. That triumph was almost unimaginable a decade ago. (The two remain in close competition for the top spot.)
In 2014, the same year that Harris joined Microsoft and Nadella became the CEO, Wall Street and consumers alike viewed the company as stuck in the past, clinging to the“shrink-wrapped” software products like Windows that put it on the map in the 1990s. Microsoft's long-stagnant share price reflected its status as an also-ran in almost every major technological breakthrough since the turn of the century, from its Bing search engine to its Nokia mobile phone division.
As the new CEO, Nadella was determined to reverse the trend and shake off the company's fuddy-duddy reputation, so he staked Microsoft's future on the Azure cloud computing division, which then lagged far behind Amazon. In his earliest all-staff memo, Nadella told employees they would need“to reimagine a lot of what we have done in the past for a ... cloud-first world .”
Microsoft salespeople pitched business and government customers on a“hybrid cloud” strategy, where they kept some traditional, on-premises servers (typically stored on racks in customers' own offices) while shifting most of their computing needs to the cloud (hosted on servers in Microsoft data centers).
Security was a key selling point for the cloud. On-site servers were notoriously vulnerable, in part because organizations' overburdened IT staff often failed to promptly install the required patches and updates. With the cloud, that crucial work was handled by dedicated employees whose job was security.
The dawn of the cloud era at Microsoft was an exciting time to work in the field of cybersecurity for someone like Harris, whose high school yearbook features a photo of him in front of a desktop computer and monitor with a mess of floppy disks beside him. One hand is on the keyboard, the other on a wired mouse. Caption:“Harris the hacker.”
As a sophomore at Pace University in New York, he wrote a paper titled“How to Hack the Wired Equivalent Protocol,” referring to a network security standard, and was awarded a prestigious Defense Department scholarship that the government uses to recruit cybersecurity specialists. The National Security Agency paid for three years of his tuition, which included a master's degree in software engineering, in exchange for a commitment to work for the government for at least that long, he said.
Early in his career, he helped lead the Defense Department's efforts to protect individual devices. He became an expert in the niche field known as identity and access management, securing how people log in.
As the years wore on, he grew frustrated by the lumbering bureaucracy and craved the innovation of the tech industry. He decided he could make a bigger impact in the private sector, which designed much of the software the government used.
At Microsoft he was assigned to a secretive unit known as the“Ghostbusters” (as in:“Who you gonna call?”), which responded to hacks of the company's most sensitive customers, especially the federal government. As a member of this team, Harris first investigated the puzzling attack on the tech company and remained obsessed with it, even after switching roles inside Microsoft.

Legal Disclaimer:
MENAFN provides the
information “as is” without warranty of any kind. We do not accept
any responsibility or liability for the accuracy, content, images,
videos, licenses, completeness, legality, or reliability of the information
contained in this article. If you have any complaints or copyright
issues related to this article, kindly contact the provider above.





















Comments
No comment