(MENAFN- Asia Times) This article is adapted from the authors' new book, Battlefield Cyber: How China and Russia are Undermining our Democracy and National Security (Prometheus, August 2023, available for preorder here ).
Recent revelations that Chinese state-sponsored hackers penetrated US critical infrastructure and have the ability to disrupt oil and gas pipelines, rail systems, and the US Navy's communications in the Pacific theater should come as no surprise. China's pursuit of digital dominance has been decades in the making.
Reveille for China's planners was sounded in the early 1990s during the Gulf War, in which the United States and its allies effortlessly toppled Iraqi forces. The first conflict of the digital era demonstrated to Chinese strategists the critical role of information technology on and off the battlefield.
Chinese leaders watched with dismay as the American military routed and dismantled the Iraqi military in what is considered one of the most one-sided conflicts in the history of modern warfare.
Going into the first Gulf War, Iraq's military was ranked fourth in the world – having ballooned to more than a
million troops who had been trained on weapons financed by the West to fight its bloody eight-year war with Iran.
The Chinese military, although larger in headcount at the time, paled in technological comparison with the forces commanded by Saddam Hussein. At the time, China's air force consisted of a few fighter jets, mostly of its J-7 model – an indigenously produced replica of the Russian 1960s-era MiG-21.
Iraq's air force, by contrast, was made up of far more advanced fighters, such as the Russian MiG-29, and its planes were supported by advanced antiaircraft missile defense systems. Yet even those advanced weapon systems proved wholly ineffective against 1990s-era American technology.
“The Chinese looked at Iraq and saw an army similarly equipped as theirs with old Soviet weaponry, and they saw how quickly the Iraqis were taken apart,” says analyst Scott Henderson of the cybersecurity firm Mandiant. Henderson was with the US Army at the time, specializing in China.
“A lot of the ease of victory had to do with the information advantage,” he says.“The Chinese looked at that as a warning to them, but also an opportunity. The Chinese realized they did not have to compete with the US plane-for-plane and tank-for-tank. They could envision how they could get to a level playing field using technology, rather than building traditional weapons.”
China's subsequent campaign of aggressive technology modernization has enabled a sprint to near parity with the United States.
Crucial to this achievement has been China's centralized economic control – over not only state-owned enterprises but also formerly private-sector companies over which the Chinese Communist Party has now asserted de facto legal control through a series of national security, intelligence, and cybersecurity laws.
The government announces openly the technologies it wants to develop. It did so in its“Made in China 2025” plan and also has done so in its 14 consecutive five-year plans. The Chinese government supports domestic companies to become global leaders in these technologies.
To that end, the Chinese military and intelligence services turn over to those companies R&D secrets obtained through cyber activities and intellectual property theft. As a result, advanced military capabilities, based on the stolen designs, are rapidly developed and then flow to the People's Liberation Army as part of the“military-civil fusion” that President Xi Jinping has declared.
The end goal of this process is to transform the PLA into the world's most technologically advanced military by 2049, the 100th anniversary of Mao Zedong's establishment of communist rule in China.
The fruits of this espionage-fueled modernization plainly have manifested themselves in China's march toward naval superiority. Since the early 1990s, China has been transforming its navy into an advanced modern force capable of contending with the US Navy. According to the US Department of Defense, China's current fleet comprises the largest navy in the world with 355 vessels.
In June 2022, the Chinese navy launched its first indigenously produced aircraft“supercarrier.” Named for China's Fujian Province, this new supercarrier forms the cornerstone of China's modern blue-water naval force. Before Fujian, the Chinese navy's two seaworthy carriers were small carriers that used ski-jump-like devices to launch planes. They were based on a 1980s-era Russian Kuznetsov-class carrier.
The newly launched Fujian, at nearly 1,000 feet in length, is based on America's recently launched USS Gerald R. Ford, as evidenced in Chinese propaganda photos showing the housings for Fujian's four electromagnetic catapults – capable of launching the ship's entire complement of aircraft in under an hour.
How China has been able to rapidly transform its Cold War-era ships to a modern and technologically advanced naval fleet can be found in a trail of digital breadcrumbs left in the networks of American companies.
As early as 2013, the Defense Science Board reported that more than 50 Defense Department system designs and technologies had been compromised by Chinese hackers. Prominently listed in its report were advanced aircraft designs and the electromagnetic aircraft launch system that recently was unveiled on the Fujian.
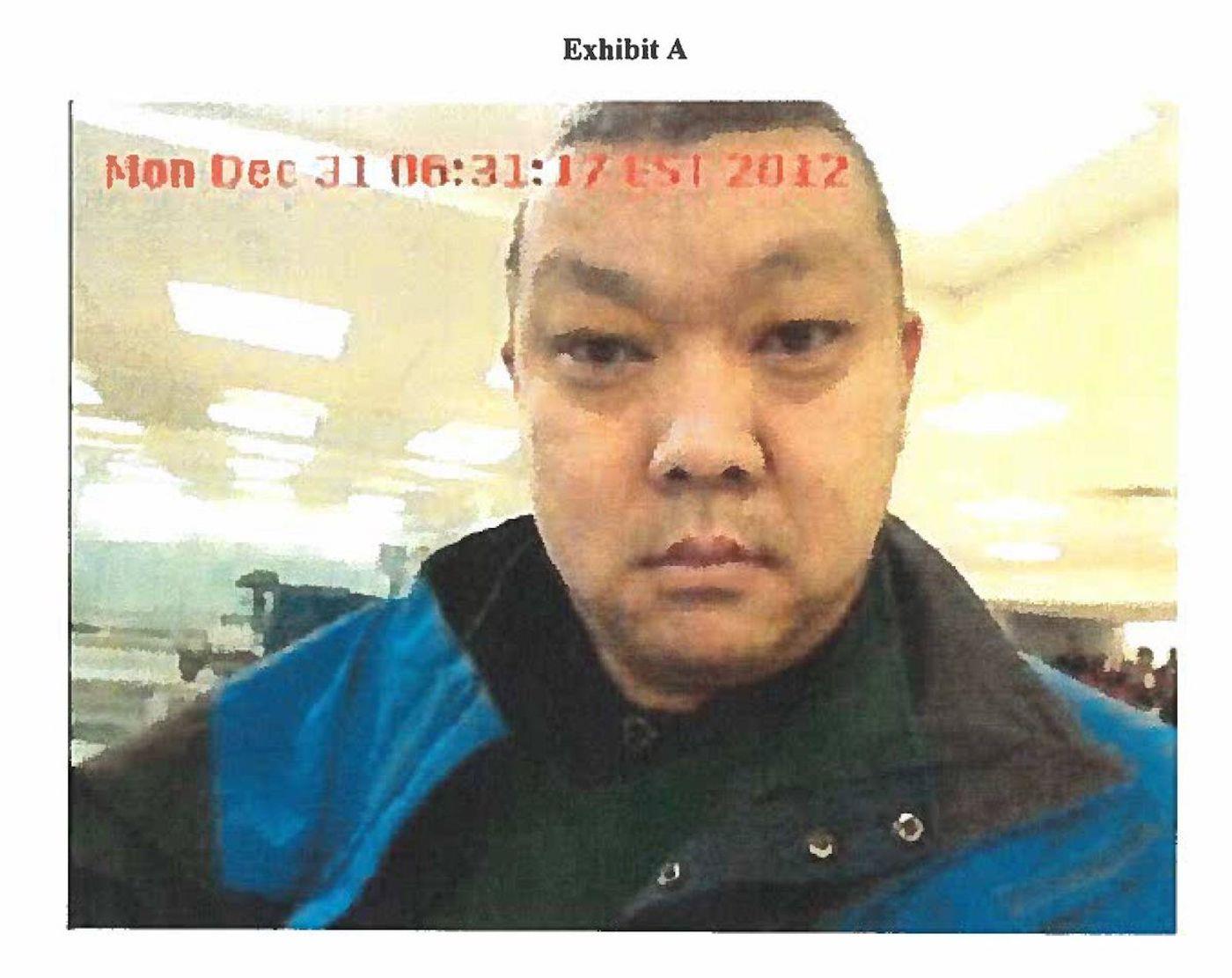
Su Bin, confessed spy. Photo: court documents
In 2014, the FBI arrested a Chinese national and permanent resident of Canada for his part in a six-year conspiracy that allowed Chinese hackers access to the networks of Boeing. In his 2016 guilty plea, Su Bin admitted to having enabled the hackers to steal sensitive military information – including information on the development of America's latest carrier-based stealth fighter, the F-35. In total, the scheme yielded the Chinese government hundreds of thousands of flight-test documents pertaining to American naval aircraft.
Penetrations were not limited to fighter jets and carriers. In 2017, a Chinese hacking group was quietly probing the network of another defense contractor. Due to the sensitivity of the program, the US government redacted the victim company's name in all official correspondence, except to verify that the company was working on sensitive programs for the US Naval Undersea Warfare Center. In the end, the Chinese hackers stole more than 600 gigabytes of data from the contractor's system.
Charged with developing next-generation submarine technologies and weapon systems, the Naval Undersea Warfare Center is based in Newport, Rhode Island. It is the Navy's focal point for all research, development, testing, and evaluation of undersea warfare capabilities ranging from autonomous submersibles to submarine communication systems to small modular nuclear reactors.
The unnamed contractor was secretly developing a supersonic anti-ship cruise missile capable of being launched from submarines.“Sea Dragon” – as the program was named – was scheduled for initial deployment on US submarines in 2020.
Considered a game changer by military experts, submarine-launched supersonic and hypersonic anti-ship missiles are incredibly difficult to shoot down and nearly impossible to evade.
But in early 2018, Chinese hackers penetrated the contractor's network and stole the Sea Dragon plans. The technology is now included in China's naval arsenal and will surely be fielded against the US Navy during any potential conflict.
Has the US come to grips with what it's facing? The recent revelation by Microsoft of Volt Typhoon – a state-sponsored cyber actor based in China – indicates there remains significant work to be done.
Plugging the holes
As a warfighter during a storied career that spanned 39 years, US Air Force General Herbert“Hawk” Carlisle led combat aviators flying some of the most advanced weapon systems on the planet. Before retiring with four stars, Carlisle rose to become commanding general of the Air Combat Command – responsible for overseeing, delivering, and maintaining all Air Force combat assets, including more than 135,000 airmen, worldwide.

General Herbert“Hawk” Carlisle. Photo: YouTube
Carlisle knew what he was talking about when he wrote in a 2020 Defense Department report
on threats to the US military's supply chain:“Our military superiority is under direct attack from our most sophisticated adversaries – nations whose cyber actors continuously target the very industry that powers the US military's technological advantage.”
After retiring, Carlisle served as the president of the National Defense Industrial Association – an organization that works with the defense industrial base, which consists of more than 300,000 companies, including major corporations such as Lockheed Martin, Boeing and Northrop Grumman as well as smaller companies.
In 2022, the association wrote in its annual report that the defense industry“faces sustained and increasing threats of intellectual property theft, economic espionage, and ransomware, among other security breaches. Data breaches, intellectual property theft and state-sponsored industrial espionage in both private companies and university labs are on an unrelenting rise.”
These warnings should be read as an SOS for US national security. For the first time, the US military can see clearly that it could be fighting an advanced Chinese adversary armed with weapons developed from stolen American technology.
Yet the Pentagon has been unable to focus sufficient attention on the threats that face its suppliers due to limited authority and resources to identify possible Chinese penetrations in its supply chain. While the Defense Department and the defense industrial base stumble through the years-long implementation of effective cyber safeguards,
Chinese cyber actors continue to pillage America's defense intellectual property.
It is critical for Americans to understand that the centralized party-state of China is undermining and exploiting the United States' current defenses against theft of military secrets and intellectual property. This alarming situation demands immediate and decisive action on two fronts.
Domestically, it is essential to bridge the longstanding libertarian divide between the public and private sectors. This will involve augmenting and enforcing cybersecurity regulations along the defense supply chain, cultivating an environment that supports cyber hygiene and the exchange of threat intelligence, as well as encouraging investment in the advancement and application of state-of-the-art security technology.
On the global stage, the United States and its allies must act assertively to hold China accountable for its cyber and corporate espionage, particularly when targeting defense technologies and critical infrastructure. Possible measures may include sanctions, international détentes and embargoes against Chinese corporations that benefit from the fruits of malicious cyber activities.
Furthermore, the global community needs to set standards of conduct concerning cyber-economic and industrial espionage. Such a collective effort would form a united front of nations ready to challenge China and impose penalties for its aggressive behavior.
As a naval officer, Michael G McLaughlin served as senior counterintelligence advisor for the United States Cyber Command, responsible for the coordination of Department of Defense counterintelligence operations in cyberspace. He is now a cybersecurity attorney and policy advisor in Washington, DC.
William J Holstein was based in Hong Kong and Beijing for United Press International and has been following US-China relations for more than 40 years. Holstein has worked for or contributed to top publications including Business Week, US News & World Report, the New York Times and Fortune. His nine previous books include The New Art of War: China's Deep Strategy Inside the United States.
Like this:Like Loading...