
Lockbit 5.0 Infrastructure Leak Reveals Exposed Servers And Domains
Security researchers have uncovered critical infrastructure details tied to the ransomware operation LockBit 5.0, exposing a publicly accessible server and domain used by the gang. The server, identified by IP address 205.185.116.233, and the domain karma0. xyz have been linked to the group's latest leak-site. The disclosure, first shared by cybersecurity researcher Rakesh Krishnan on 5 December 2025, represents a major operational security failure for the ransomware collective.
The exposed server is hosted under AS53667, a network previously flagged for hosting illicit activities. Its web interface displays a DDoS protection banner labelled“LOCKBITS.5.0,” underscoring its role in LockBit's infrastructure. WHOIS records show that karma0. xyz was registered in April 2025, with Cloudflare nameservers and privacy protections listing a Reykjavík contact address, while its domain status restricts transfers-suggesting attempts to harden control under scrutiny.
Port scans of 205.185.116.233 reveal multiple open services, including FTP on port 21, Apache HTTP on port 80, RDP on port 3389, WinRM on port 5985, and various file-sharing services. The presence of RDP access is particularly concerning, as it provides a high-risk vector for remote intrusion and could enable actors to hijack the server or use it for further attacks.
The exposure coincides with a wider resurgence of LockBit following its high-profile disruption in early 2024 under Operation Cronos. Despite that takedown-and a May 2025 leak of LockBit's administrative panel and affiliate data-the group has bounced back with its 5.0 variant. According to security vendor Check Point Research, the group carried out multiple attacks across continents in September 2025, affecting both Windows and Linux systems, underlining that its infrastructure and affiliate network remain active.
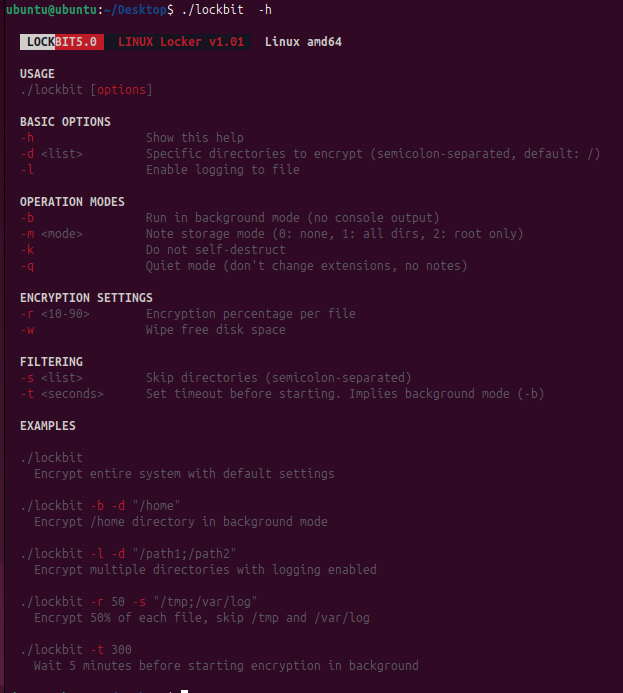
See also Saudi AI Infrastructure Giants Unite for Multi-Gigawatt Data HubThe technical improvements in LockBit 5.0 have drawn attention from defenders and researchers. According to analysis by Flashpoint and the security firm Trend Micro, the new variant employs a two-stage modular execution model: a stealth loader followed by the main payload. It leverages techniques such as obfuscated control flow, dynamic API resolution, DLL reflection, and ETW patching to evade detection. The ransomware supports Windows, Linux and VMware ESXi platforms, offering affiliates multiplatform capabilities rarely seen in earlier versions.
LockBit 5.0's encryption process introduces randomized 16-character file extensions and optional“invisible mode,” which omits extensions and ransom notes-making detection and recovery more difficult. The payload can also disable or terminate security services, wipe event logs after execution, and target entire network environments including virtualised systems.
Notice an issue? Arabian Post strives to deliver the most accurate and reliable information to its readers. If you believe you have identified an error or inconsistency in this article, please don't hesitate to contact our editorial team at editor[at]thearabianpost[dot]com. We are committed to promptly addressing any concerns and ensuring the highest level of journalistic integrity.
Legal Disclaimer:
MENAFN provides the
information “as is” without warranty of any kind. We do not accept
any responsibility or liability for the accuracy, content, images,
videos, licenses, completeness, legality, or reliability of the information
contained in this article. If you have any complaints or copyright
issues related to this article, kindly contact the provider above.

















Comments
No comment